### Multiple Unauthenticated Vulnerabilities in PolarRx5 GNSS Receiver

PolaRx5 is a versatile and robust multi-frequency GNSS reference receiver. The
unique design of its tracking provides measurements with the lowest noise on
the market while constantly monitoring and protecting against interference,
multipath and other environmental effects.
The PolaRx5 is developed specifically to support the most demanding
applications for the earth science community offering a select range of
advanced features which enable maximum accuracy and functionality. Powered by
Septentrio's next generation multi-frequency engine, the PolaRx5 offers 544
hardware channels for robust and high quality GNSS tracking.
_\--https://www.septentrio.com/en/products/gnss-receivers/reference-
receivers/polarx-5_

```
The tested version of the device was **PolarRx5-3022831**
```
## **`1. Path Traversal`**
```
Affected URLS:
```
- http://x.x.x.x/ascii=ldi%2CDSK1%2C../../../../
- http://x.x.x.x/status?p=../../../../../../../../../../../../../../../../../../../../../../../some_internal_file
```
Description:
```
```
In an unauthenticated session, you can browse many sections of the web associated to the device,
there is a section where you can list and download files from the filesystem, these files are
located at the "Disk Contents" subsection of the "Logging" menu
```

```
```
Looking for the requests that the webpage generates I've noticed that in a parameter of a
request the name of the folder that I've clicked in the frontend was reflected there:
```
```

```
So basically I changed the file name with the typical path traversal payload:
```

```
And amazingly the contents of the filesystem's root was displayed in clear text
```

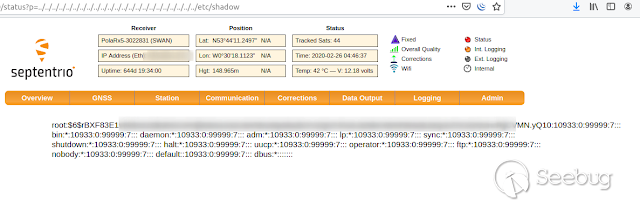
## `2. Local File Inclusion`
```
Affected URLs: http://x.x.x.x/status?p=filename
```
```
Description:
```
```
This vulnerability is similar to the last, also unauthenticated, but with the difference that
```
```
I was able to retrieve the content of a system file.
```
```
First we must go to the URI /scr?fra0=afterupgrade.html, there is a link to the device
```
```
identification info, when we click the link we can notice that in the URL now the Path is
```
```
"status" with a parameter named "p"
```


```
On this parameter ("p"), if we put some path traversal payloads and appending at the end
```
```
for example "/etc/shadow", we can retrieve the contents of the mentioned file
```
[](https://images.seebug.org/1583460609713-w331s)
```
[@xpl0ited1](https://www.twitter.com/xpl0ited1)
```







暂无评论