### - Eaton Authenticated Stored Cross Site Scripting (CVE-2020-7915)
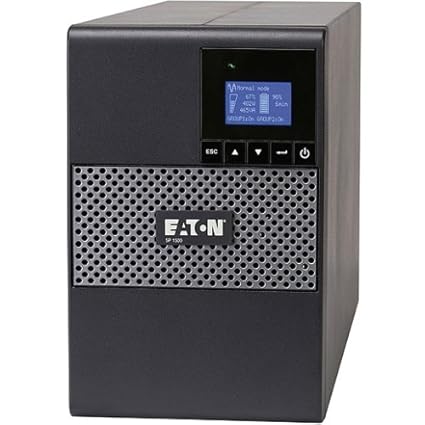
Eaton is a company dedicated to the electrical and industrial power management
solutions. In this case in particular I'm going to talk about the Eaton 5P
1.
In the System menu, there's the "Ubicacion SAI" parameter. This parameter is
just the location name of the UPS, this can be modified by the administrator
with any name.
The parameter "Ubicacion SAI" is vulnerable to XSS attacks, because the data
is not validated properly.
In order to exploit, you only need to modify the name in the parameter and use
the most simple XSS script. After that, save the changes with the Guardar
buttom. The webapp will reload it self and it'll pop up the alert in the
script.

As
you can see, that script is being inserted in the right upper banner, at the
right of the name of the UPS.



CVE-2020-7915








暂无评论