While investigating the Grandstream UCM6202 IP PBX, Tenable discovered a few SQL injections that an unauthenticated remote attacker could use to obtain user passwords.
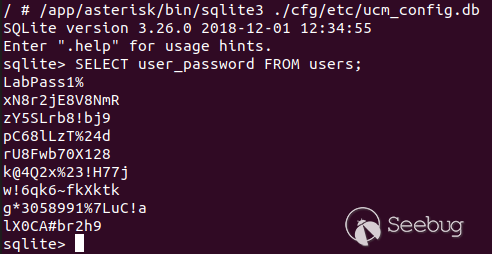
#### CVE-2020-5723: Cleartext Storage of Sensitive Information ([CWE-312](https://cwe.mitre.org/data/definitions/312.html))
The UCM6200 series stores unencrypted user passwords in an SQLite database. This could allow an attacker to retrieve all passwords and possibly gain elevated privileges.
#### CVE-2020-5724: Unauthenticated Remote Blind SQL Injection
The webserver's websockify endpoint is vulnerable to SQL injection when the *challenge* action is invoked. The username provided by the unauthenticated remote attacker is used to build an SQL query into the users table. Furthermore, successful queries and unsuccessful queries generate different responses from the server. As such, an unauthenticated remote attacker can recover user passwords.
A proof of concept can be found in our [GitHub repository](https://github.com/tenable/poc/blob/master/grandstream/ucm62xx/websockify_challenge_injection.py).
#### CVE-2020-5725: Unauthenticated Remote Blind SQL Injection
The webserver's websockify endpoint is vulnerable to SQL injection when the *login* action is invoked. The username provided by the unauthenticated remote attacker is used to build an SQL query into the users table. As such, by using time based attacks, an unauthenticated remote attacker can recover user passwords.
A proof of concept can be found in our [GitHub repository](https://github.com/tenable/poc/blob/master/grandstream/ucm62xx/websockify_login_injection.py).
#### CVE-2020-5726: Unauthenticated Remote SQL Injection via CTI
The CTI server on port 8888 is vulnerable to SQL injection when the *challenge* action is invoked. The username provided by the unauthenticated remote attacker is used to build an SQL query into the users table. Furthermore, successful queries and unsuccessful queries generate different responses from the server. As such, an unauthenticated remote attacker can recover user passwords
A proof of concept can be found in our [GitHub repository](https://github.com/tenable/poc/blob/master/grandstream/ucm62xx/cti_injection.py).
### Solution
Upgrade to 1.0.20.22 or newer.
### Additional References
<http://firmware.grandstream.com/Release_Note_UCM6xxx_1.0.20.22.pdf>
<https://github.com/tenable/poc/blob/master/grandstream/ucm62xx/websockify_challenge_injection.py>
<https://github.com/tenable/poc/blob/master/grandstream/ucm62xx/websockify_login_injection.py>
<https://github.com/tenable/poc/blob/master/grandstream/ucm62xx/cti_injection.py>
### Disclosure Timeline
March 23, 2020 - Tenable reports unauth password disclosure websockify SQL injection.
March 24, 2020 - Grandstream acknowledges Tenable and escalates the report.
March 25, 2020 - Grandstream asks Tenable to test against 1.0.20.20.
March 25, 2020 - Tenable replies 1.0.20.20 is vulnerable.
March 27, 2020 - Tenable reports two additional SQL injections.
March 27, 2020 - Grandstream acknowledges and asks which version Tenable tested against.
March 27, 2020 - Tenable replies 1.0.20.20
March 30, 2020 - Grandstream informs Tenable that they've patched the issues in 1.0.20.22.


暂无评论